
AI tools like Microsoft 365 Copilot have moved from hype to expectation. SMB leaders now expect their teams to work faster and smarter with AI support — drafting content, extracting insights from meetings, and turning data into decisions. But whether Copilot delivers on that promise depends on something most businesses overlook.
---------------------------------------------------------------------------------------------------------------------
Before you flip the switch on AI, there is a critical question every business owner must answer: Is your data actually ready for it?
Deploying Copilot without first organizing and securing your information is like hiring a world-class executive assistant and handing them a filing cabinet that hasn’t been organized in a decade — with sensitive payroll records sitting in plain view. AI can only work with what it’s given. If your data is scattered, duplicated, or poorly governed, the output will reflect it.
To get real value from Copilot, you need more than a subscription. You need data readiness.
What is Data Readiness for Copilot?
Microsoft 365 Copilot doesn’t just "know" things; it works by scanning your existing business ecosystem—your emails, Teams chats, SharePoint files, and OneDrive documents—to generate answers. This process is called grounding.
Data readiness is the practice of ensuring that the information Copilot accesses is accurate, organized, and properly restricted. If your data is clean and well-governed, Copilot becomes a powerhouse. If it’s messy, Copilot can become a liability.
The Hidden Risks of an "Unready" Environment
Many SMBs operate on a trust-based digital culture where folders are often shared more broadly than necessary. While this might feel efficient in a small office, it creates two major risks when AI enters the picture:
One, the Oversharing Trap
Copilot respects your existing security permissions. The problem? Many businesses have broken permissions they don't know about. If a sensitive document (like a salary list or a pending termination notice) is accidentally set to "Internal – Anyone can view," Copilot can find it. If an employee asks, "What is the average salary in the marketing department?", Copilot will dutifully provide the answer based on that file.
Two, the Digital Junk Factor
AI is only as good as the information it consumes. If your SharePoint is cluttered with five different versions of a 2023 strategy deck, Copilot might pull data from "v1_OLD" instead of the final version. This leads to hallucinations or simply outdated, incorrect advice that can find its way into your client-facing documents.
Three Steps to Get Your Data AI-Ready
You don’t need to be a data scientist to prepare your business for Copilot. Focus on these three pillars:
I. Data Hygiene (The Spring Cleaning)
Before inviting AI into your files, it’s time to archive. Delete or move old document versions to a legacy folder that Copilot doesn't index. Focus on keeping your active folders lean and mean—containing only current, verified information.
II. Permissions Audit (The Security Check)
Check your "Shared with Everyone" settings. A proactive IT strategy involves moving toward the Principle of Least Privilege. This means employees have access only to the data they need to do their jobs. Not only does this protect you from internal leaks, but it also ensures Copilot stays in its lane.
III. Data Classification
Labeling your data—such as Public, General, or Highly Confidential—helps the system understand what is sensitive. When you classify your data, you add a layer of protection that travels with the file, ensuring that even the smartest AI knows which documents require extra care.
The Path to Productivity
Preparing for Copilot isn't just about avoiding risks; it’s about maximizing your investment. When your data is structured correctly, the AI becomes incredibly sharp. It stops being a search tool and starts being a strategic partner that understands your business's unique voice and history.
Managing this transition can feel overwhelming for a busy team. This is where a proactive IT partner becomes invaluable. By conducting a readiness assessment, an expert can identify overshared files, clean up your permissions, and ensure your cloud environment is a fortress—not a free-for-all.
The goal isn't just to use AI; it's to use AI safely and effectively.

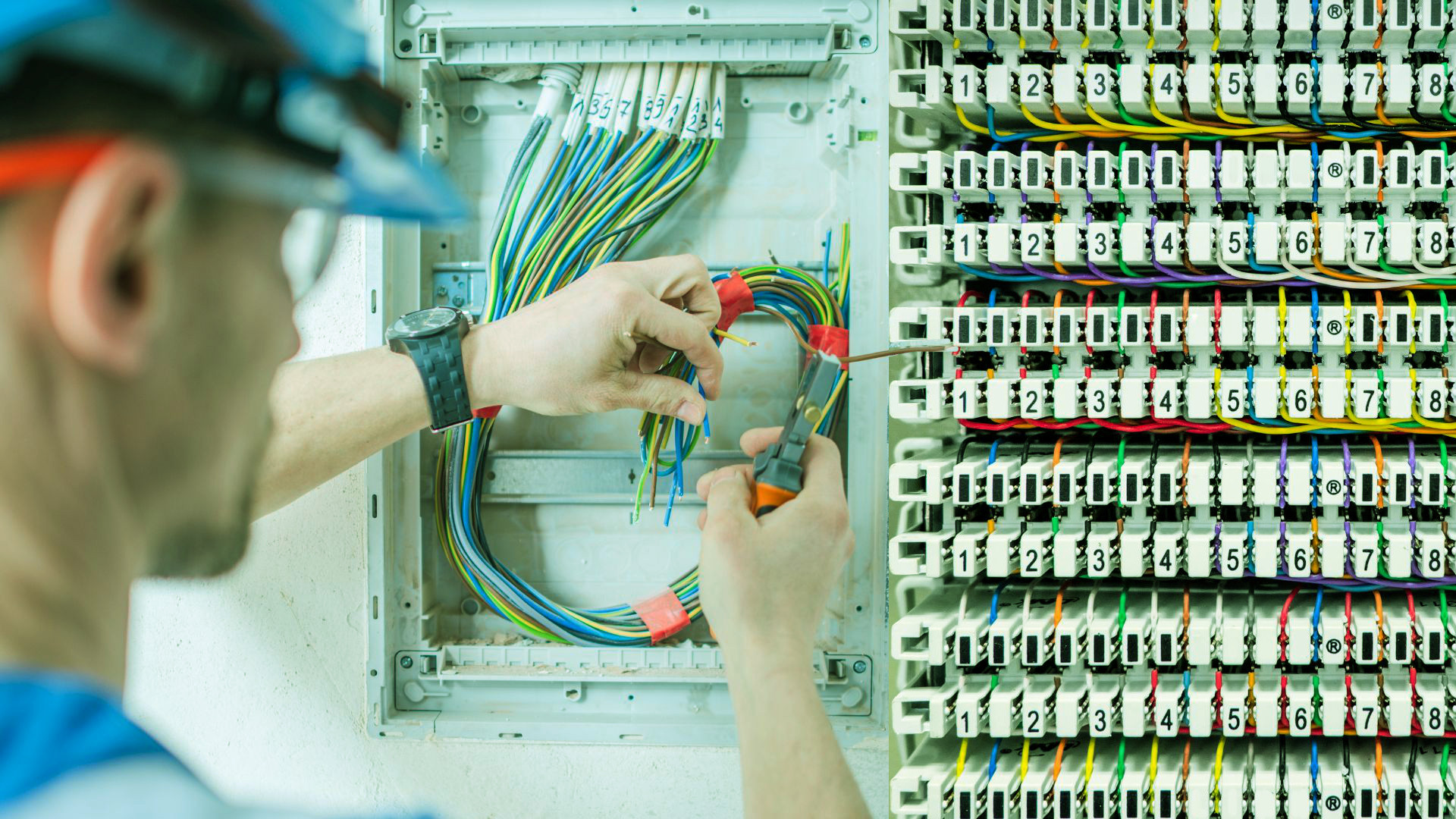 Dependable IT support is essential for all firms in the current digital world. Having the right technology in place is crucial to remain efficient, secure, competitive, or current in your field. In the end, you also need competent In-House IT specialists to manage all these technological requirements.
Dependable IT support is essential for all firms in the current digital world. Having the right technology in place is crucial to remain efficient, secure, competitive, or current in your field. In the end, you also need competent In-House IT specialists to manage all these technological requirements. Every business owner understands the importance of physical security—locking the doors, setting the alarm, and controlling who has a key to the office… but, what about your digital assets? Your customer records, financial data, and intellectual property are far more valuable than the office furniture, yet often lack the same level of protection.
Every business owner understands the importance of physical security—locking the doors, setting the alarm, and controlling who has a key to the office… but, what about your digital assets? Your customer records, financial data, and intellectual property are far more valuable than the office furniture, yet often lack the same level of protection.


 Microsoft Copilot is an AI assistant seamlessly integrated into the Microsoft 365 apps your business already uses. Think of it as a highly capable assistant sitting in on your meetings and helping with your daily tasks, but without the overhead. Instead of sifting through hours of meeting recordings or long email threads, Copilot does the heavy lifting, helping your team focus on what really matters. It's designed for small to medium-sized businesses that want to boost productivity without a steep learning curve.
Microsoft Copilot is an AI assistant seamlessly integrated into the Microsoft 365 apps your business already uses. Think of it as a highly capable assistant sitting in on your meetings and helping with your daily tasks, but without the overhead. Instead of sifting through hours of meeting recordings or long email threads, Copilot does the heavy lifting, helping your team focus on what really matters. It's designed for small to medium-sized businesses that want to boost productivity without a steep learning curve.
 AI is quietly changing the game for businesses in 2025—but not everyone is ready. Some business owners are already seeing massive growth from AI-driven insights and automation, while others don’t even realize they’re falling behind. If you're running a business in the Tri-State Area, you've likely heard lots of buzz about AI. Maybe you dismissed it, thinking it’s just for big tech companies, but guess what? It’s a lot more accessible than you think!
AI is quietly changing the game for businesses in 2025—but not everyone is ready. Some business owners are already seeing massive growth from AI-driven insights and automation, while others don’t even realize they’re falling behind. If you're running a business in the Tri-State Area, you've likely heard lots of buzz about AI. Maybe you dismissed it, thinking it’s just for big tech companies, but guess what? It’s a lot more accessible than you think!

 Luckily, most people will, if they have an eligible device, upgrade to Windows 11. The promise of new innovations with productivity, connectivity, and creativity is now a reality. For those who can't upgrade due to their device not having the right specs, and who don’t want to buy a new device, Windows 10 will be the right choice. Microsoft said it will continue to support Windows 10 until October 2025, and there will even be updates to it later this year.
Luckily, most people will, if they have an eligible device, upgrade to Windows 11. The promise of new innovations with productivity, connectivity, and creativity is now a reality. For those who can't upgrade due to their device not having the right specs, and who don’t want to buy a new device, Windows 10 will be the right choice. Microsoft said it will continue to support Windows 10 until October 2025, and there will even be updates to it later this year.



 Cyber criminals don’t just slip into your network with the help of some serious hacking skills. In fact, there’s a much simpler way to do that... through your employees.
Cyber criminals don’t just slip into your network with the help of some serious hacking skills. In fact, there’s a much simpler way to do that... through your employees.  small businesses and tech giants are experiencing the rippling impact of a data breach.
small businesses and tech giants are experiencing the rippling impact of a data breach.